Meltdown & Spectre the last Opera 68.0.3618.104 vulnerability
-
andrew84 last edited by andrew84
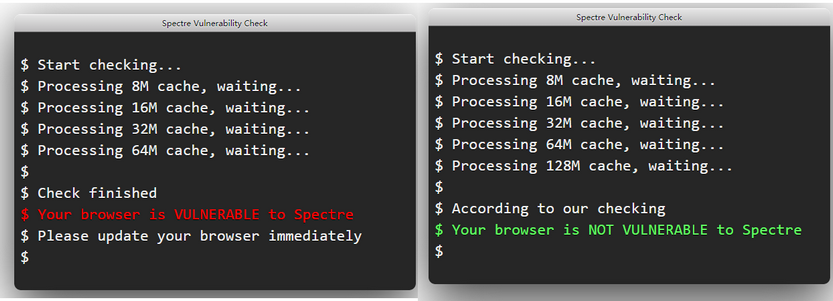
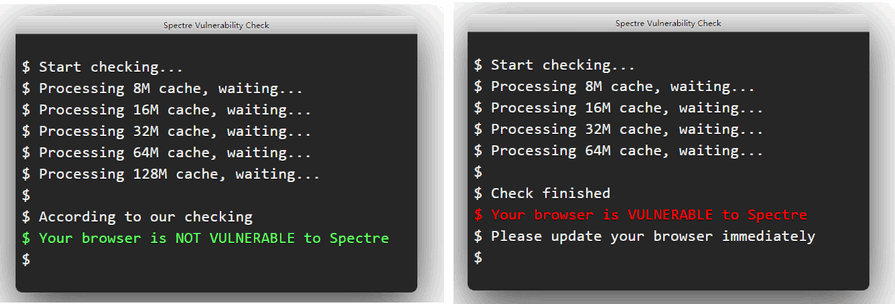
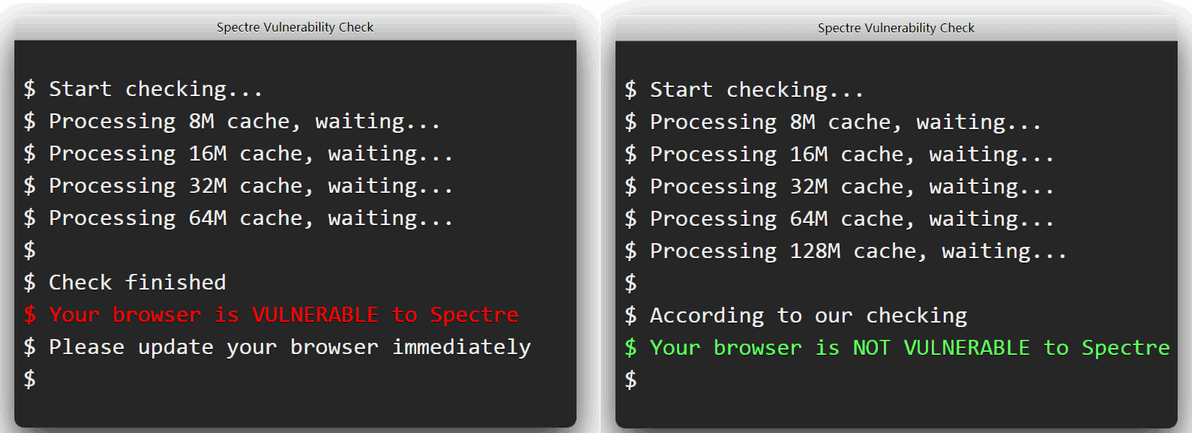
I have the same in latest MS Edge build (Canary), if 128 cache was scanned, then all is fine.
-
anastasia-mx last edited by
@leocg said in & Spectre the last Opera 68.0.3618.104 vulnerability:
Did you check with a clean profile?
if you delete all the settings, it will be very bad and I will need to configure a lot from the beginning
@donq said in & Spectre the last Opera 68.0.3618.104 vulnerability:
What offline scanner says? https://www.grc.com/inspectre.htm
Meltdown & Spectre - NO!, NO! updates strongly slow down the system, I do not want to put them, I have hope for the browser itself.
@leocg said in & Spectre the last Opera 68.0.3618.104 vulnerability:
What about other Chromium based browsers?
not used by others Chromium based browsers. I only use Mozilla - everything is fine in it, there is no vulnerability.
any other sites to check for vulnerabilities?
-
leocg Moderator Volunteer last edited by
@anastasia-mx Since Opera is a Chromium based browser, you need to also check with other Chromium based browsers to have a valid comparasion.
-
leocg Moderator Volunteer last edited by
@anastasia-mx A clean profile would help checking if the problem is not being caused by a broken profile.
-
donq last edited by
IIRC at least some (theoretical) browser attacks were based on precision timing in javascript and mitigation was done by randomizing JS timing errors - all such behavior is seated deep inside JS engine and should not be related to broken profile. Well, there likely are some JS flags, which may alter engine behavior - and you may search or ask on chrome/chromium forums, have they changed anything related to spectre or JS timings.
I have not heard about (widespread) real-word exploits, based on spectre (or meltdown). I would think such kind of vulnerabilites can be used for targeted attaks, where every bit of information can be valuable; for generic attakcs (to take PC over) this is a bit hard and unpredictable to use - of course I may be wrong here.
-
johnd78 last edited by
I found a blog comment from the Opera developers. https://blogs.opera.com/desktop/2018/01/opera-50-0-2762-67-stable-update/
-
andrew84 last edited by andrew84
@johnd78 said in Meltdown & Spectre the last Opera 68.0.3618.104 vulnerability:
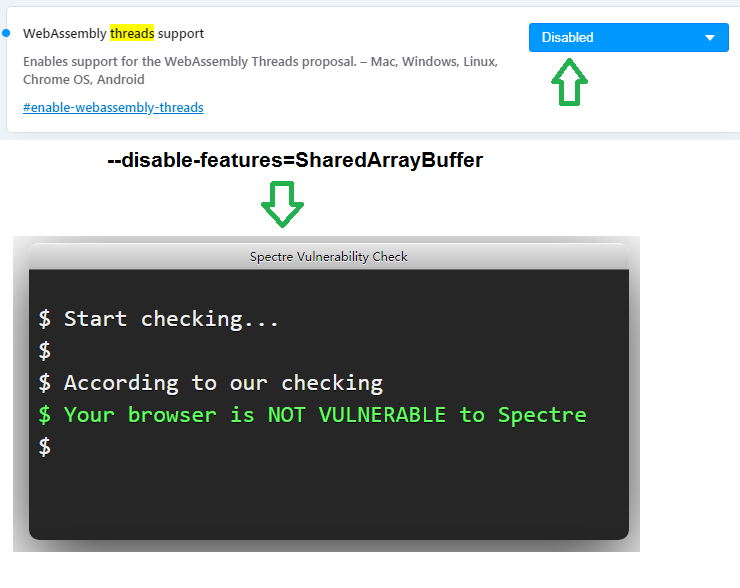
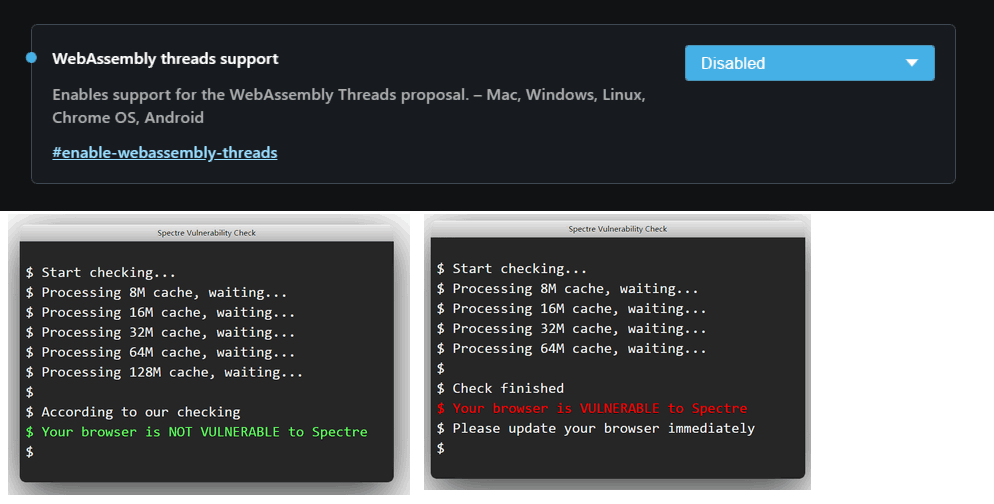
opera://flags/#enable-webassembly-threads
I disabled it, but in my case the result is still random (Portable 68.0.3618.104)
-
donq last edited by donq
@andrew84 said in Meltdown & Spectre the last Opera 68.0.3618.104 vulnerability:
Maybe the test itself is not stable. And my processors can't be called as 'modern' like it is said in the blog post's explanation.
The vulnerability itself is not 'stable'

Code in test script is a bit over my understanding, but it could be unstable either.To read protected memory areas CPU cache is cleared, code is tricked to execute speculative read from protected area (which is discarded and thus not giving error - but data is already loaded into cache) and then some other memory addresses are read - read timing depends on cache containig specific data. Some information can be leaked even using somewhat random timing - I think this is exactly what you experience.
-
anastasia-mx last edited by
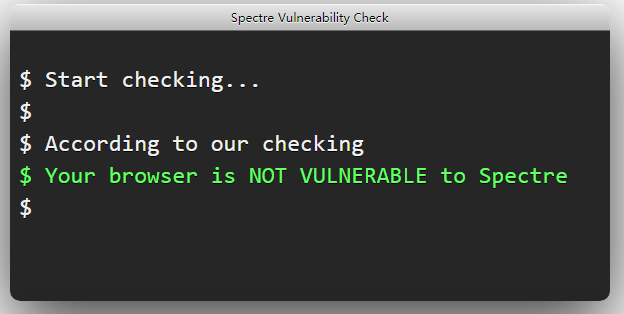
@johnd78 I used the "WebAssembly threads support" = "disabled" flag and started the program opera with the key --disable-features=SharedArrayBuffer as a result, the problem is resolved and the browser is no longer vulnerable.
can you explain what these parameters are and why they were enabled if this leads to a vulnerability?
 .
.