CSS injection in Opera for Mac
-
A Former User last edited by
Hi,
I am experiencing malicious CSS injection in Opera for macOS.
I am running the latest version 66.0.3515.103 on macOS 10.14.6.Below, you can see that CSS is injected as the last <head> child tag attribute.
This is the same on every website that I visit.-
I reset the browser, uninstalled all extensions. The injection still takes place.
-
It is only see on Opera, not on Opera Developer which I also have installed on my computer.
Chrome, Firefox are exempt of this injection.
Do you have an idea where from this malicious code is injected from?
What should I do?
Thanks,
L.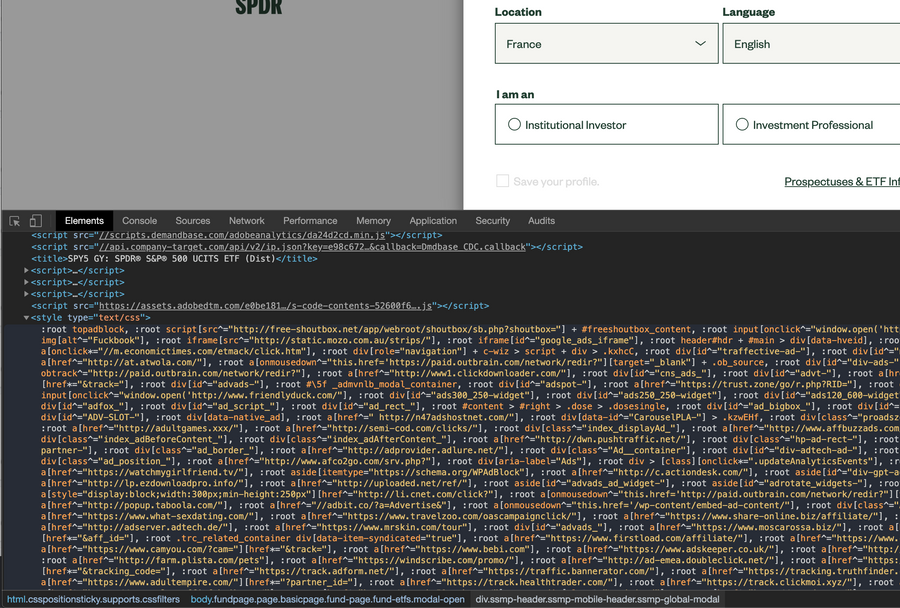
-
-
A Former User last edited by
I did search in the forum archive but could not find anything related to CSS injection. To me, this looks like malicious CSS, as you can see many scam website URLs are listed.
-
A Former User last edited by A Former User
Found it: https://forums.opera.com/topic/25957/am-i-infected-by-a-malware.
It's very weird and I feel not safe having this scam websites added as CSS injection in my pages source code. I see porn website URLs everytime I do some debugging, or I have to display ads... of course I can deactivate the ad blocker on sites I am developing on, but still a very strange dilemma.
Thanks for your help @leocg
-
A Former User last edited by
@lourou
This is not malware, but CSS rules of the internal adblocker preventing display of porn ads etc. Basic structure of rules is:root a[href^="https://adclick.g.doubleclick.net/"] { display: none !important; }which only searches for evil URLs to make bad links invisible.